Microsoft’s latest report has paved the way for cloud-based services in recent years. Overall, product-based revenue was stable at $ 15.8 billion a year ago, but services grew 23% to $ 21.4 billion. It is supported by the fast-growing business ...
Password hacks are one of the common cybersecurity threats for businesses and individuals alike. Hackers seem to devise new ways to hack into networks, devices and systems, and this can have devastating consequences for an enterprise. Data theft is just ...
Due to the spread of COVID-19, several business owners have sought exemption from paying GST for the period during which the lockdown is in force. An exemption from paying GST would grant businesses much-needed relief and may work to assist ...
The regular use of data eraser software is a must in the modern age. A data breach could potentially put your business or agency on the hook for millions of dollars in damages. Let’s take one simple example. If you’re ...
When we find the tool you want to work with, the first point you have to see is whether we can study the competition. The competence of any business gives us the advantages of our current positioning situation, and of ...
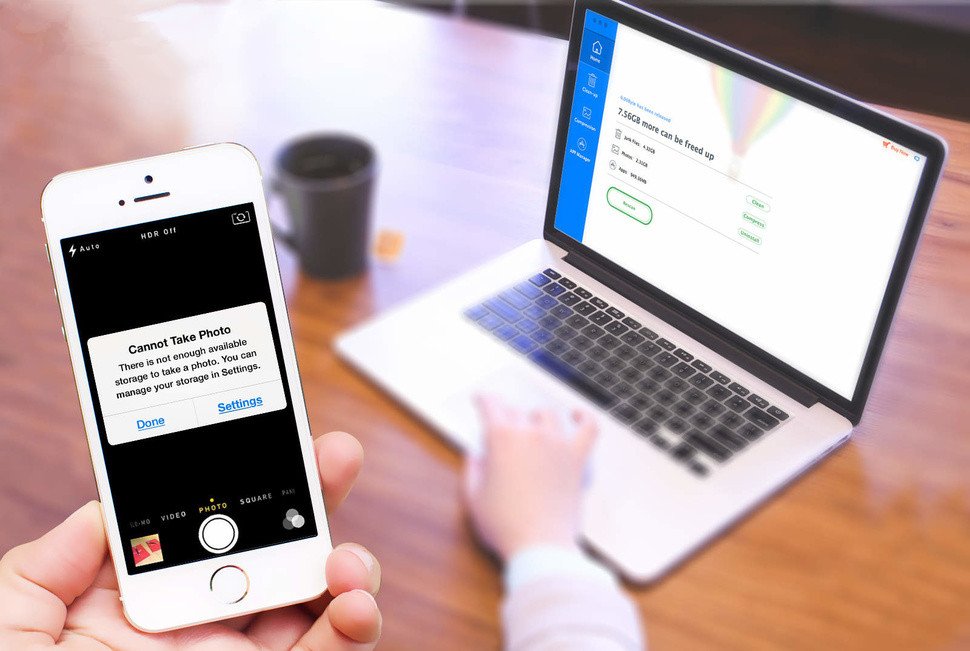
One integral aspect of photography is photo editing. For both hobbyist and professional photographers, photo editing helps you to achieve a fantastic result, making your photography experience all the more enjoyable. Varieties of image enhancement software exist today in the market; however, ...
The need for a system for a jeopardized ship to look for help while it is stranded in the center of an ocean has actually been felt ever since the first trip happened. Sailors, because long, have used one or ...
The website has become an important part of your day-to-day business. Web design and development is increasing at an important rate. The website tends to have a significant impact on daily business. As a result, most of the businesses today ...
Digital Forensics is the process of investigating various digital media or electronic devices with the aim of discovering and studying the available or ‘hidden’ data. The collected data is further used as useful evidence. In short, Computer Forensics makes it ...
The appropriate protection of critical infrastructure is almost impossible without the implementation of CCTV surveillance cameras in the contemporary period. Day and night monitoring of security cameras helps and enables the security personnel to take appropriate action on incidents of ...